You knew where this was heading.
In our previous articles we identified a constellation of front companies for APT activity in Hainan and a computer science specialist at Hainan University who is linked to one of the companies. We named the individuals that we could identify as working for these companies, including one that we know to be Hainan resident Ding Xiaoyang who had used his telephone number on a job advert using the name ‘Mr Chen’.
Having identified a network of interlinked technology and information security companies in Hainan, looking at other job adverts posted by the companies is illuminating…
South China Sea Penetration (Testing)
Considering these are high-tech companies advertising for penetration testers, software development engineers, and network engineers, of course the logical next set of job adverts that we expected to find were for … specialist translators?
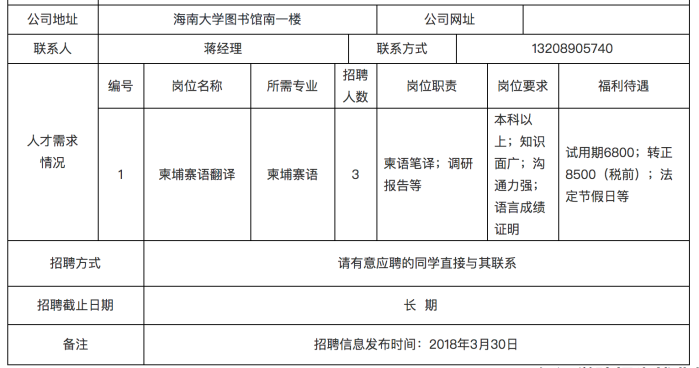
Hainan Xiandun posted multiple adverts for English translators between 2014 and 2018, such as this one on the Hainan University website:

An English language translation service in-house at a high-tech firm may meet a legitimate business need. Less likely is for a Hainan technology firm to need its own in-house Cambodian linguists. But, in March and April 2018, Hainan Xiandun was recruiting Cambodian linguists to join their team. Remember those dates, they will be important later.
Additionally, a spreadsheet published by the Shanghai International Studies University shows that Hainan Tengyuan was advertising for Indonesian and English translators.

And of course let’s not forget Sugar, who we previously identified as a Vietnamese translator at Hainan Kehua.
APT40
Which brings us to this report by FireEye on TEMP.Periscope, also know as APT40.
FireEye has examined a range of TEMP.Periscope activity revealing extensive interest in Cambodia’s politics, with active compromises of multiple Cambodian entities related to the country’s electoral system. This includes compromises of Cambodian government entities charged with overseeing the elections, as well as the targeting of opposition figures. This campaign occurs in the run up to the country’s July 29, 2018, general elections. TEMP.Periscope used the same infrastructure for a range of activity against other more traditional targets, including the defense industrial base in the United States and a chemical company based in Europe. Our previous blog post focused on the group’s targeting of engineering and maritime entities in the United States.
The report shows a world map highlighting the targets of APT40. This includes a number of English speaking countries, Indonesia, Vietnam, and Cambodia.

APT40 conducted a series of compromises of Cambodian targets in the run up to the July 2018 Cambodian election. Did you remember those dates? Between March and April 2018 Hainan Xiandun, a front company with specialist network and penetration engineers, was recruiting Cambodian linguists.
112[.]66[.]188[.]28
FireEye have also reported that APT40 actors are based in China, using computers configured with Chinese language settings.
This report also shows APT40 using IP address 112[.]66[.]188[.]28 which resolves to, guess where, Hainan.

So what?
Mr Ding and Mr Gu could be busy Hainan based individuals simultaneously running multiple companies that have specialisms spanning from penetration testing and software development to the translation of Cambodian guidebooks and Indonesian literature.
But they aren’t.
Hainan Xiandun Technology Development Company is APT40.
Hainan Xiandun, and the other front companies that we have identified, recruit hackers to compromise overseas targets and linguists to help them with their attacks and translate their stolen material. Industry reporting shows APT40 has used an IP address in Hainan and attacked South East Asian targets.
Mr Gu brings the academic links, but what does Mr Ding bring?
2 thoughts on “Hainan Xiandun Technology Company is APT40”
Comments are closed.